Many organizations are taking their cybersecurity of Operational Technology (OT) more seriously. Some organizations that recognize the unique nature of OT have either embedded OT cybersecurity staff within their IT security groups or gone all the way and created purpose-built OT security teams. Others are just starting to make sense of all this and are leaning on their IT groups to provide support.
I have witnessed the latter, but have been fortunate to build a purpose-built OT cybersecurity group in rail. Regardless of what an organization is doing, it is usually IT cybersecurity staff being thrust into the world of OT more and more.
For those of you in IT cybersecurity now entering the world of OT, here are some things to help you transition.
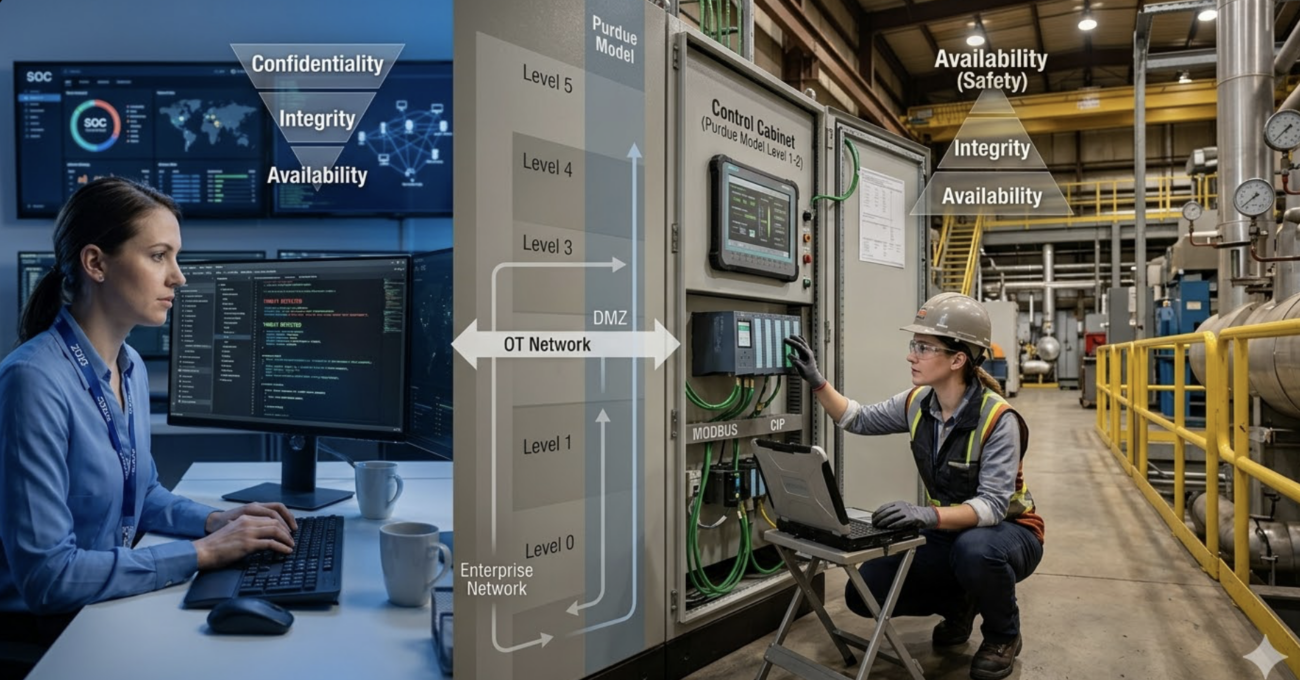
Recognize and respect that the cybersecurity paradigm is different. We have all heard this over and over by every pundit, but they are right. IT systems are about data—ensuring confidentiality and integrity before availability—while OT systems are about control of the physical world, ensuring availability and safety before confidentiality and integrity. This is counterintuitive at first, but crucial if you want to be successful.
Just because there are servers, networks, and software—or in other terms, IT—doesn’t mean that it is IT. It is OT with IT components; don’t forget that. Use your experience protecting those IT components, but remember the paradigm is different. There is no way you are going to patch servers and operating systems that host SCADA applications at the same rate as in IT environments. I have personally seen what happens when a Windows or Linux update goes south and the impact it has on operations. That is why the testing required is more rigorous and often follows a strict engineering process, which takes time and effort. Be tactful and cognizant of what it takes teams to perform even the simplest updates to their systems when recommending controls and processes. Just because it worked in IT doesn’t mean it is functionally possible in OT.
Context matters—understand it. In OT, just like in IT, some assets are more critical than others and require more protection, and sometimes they are so critical that they require less. Let me explain. In critical infrastructure, the most critical systems are those that have a direct relationship to service or safety. The natural instinct is to put the most controls on them due to how important they are. In most cases, you would be correct—but there are instances where adding cyber controls can make a system less safe or less available, which the business can’t tolerate. Remember, the paradigm is different.
An example is passwords. These are low-hanging fruit, and naturally all equipment and systems should have them. But what if a password on a piece of key safety equipment made the system less safe? How could a password make a system less safe? We are keeping unauthorized users from accessing the equipment, so it should be safer—but what if the password itself impacts the safety case and now the whole system, not just the equipment, is less safe? Did you consider that having a password initially makes the equipment less available? In an emergency situation, when that equipment must be accessed to avert a dire situation, and maintenance staff don’t know the password or need to log into a password vault—what happens? Could someone get hurt? Is that tolerable?
Now, this is an over-the-top example, but it highlights the considerations that must be made. Understand the industry you are in, the system being discussed, and the impact before providing cybersecurity guidance.
These are just a few things I learned when transitioning from IT to OT. Hope it helps you on your journey.